Proving Trust in a Zero-Trust World: The Power of Digital Attestations
Anchor your content to verifiable sources with digital attestations.

In a technology environment where information travels faster than ever, we see countless references to blogs, research papers, and corporate reports. Yet, how do we ensure that an article, whitepaper, or financial summary is genuinely based on the sources it cites? Enter digital attestations—an approach that anchors an analysis to its references, providing cryptographically verifiable proof that your text does indeed come from reputable materials.
For example, the snippet below provides a crisp analysis of Amazon’s “Are Right, a Lot” Leadership Principle, verified against the original source. While this post doesn’t include the tamper-proof record link, the original analysis includes a digital badge that points to a non-repudiable record containing the digital signature.
Leaders blend strong judgment and instincts with active self-scrutiny—seeking diverse perspectives and challenging their assumptions—to stay both accurate and adaptable. Source: Amazon Leadership Principles
If you want to deliver content that people can trust, your work must stand on a solid foundation of verifiable sources. Digital attestations help you meet this need, offering anyone the ability to check whether an analysis is faithful to the source it cites. In a zero-trust world, such verification is integral. Let’s walk through the essential features you can implement—and why they matter.
Why Digital Attestations?
Trust and Transparency
Historically, we’ve relied on bare hyperlinks or file references to claim authenticity. But that only goes so far. A digital attestation does more:
- Creates a cryptographically signed record tying your text to the source, ensuring any tampering is immediately detectable.
- Encourages transparency by embedding verification data—like how many matching tokens or phrases exist—directly in the attestation.
Streamlined Compliance and Auditing
In many industries—finance, healthcare, government—documents must withstand rigorous audits. A tamper-proof attestation that confirms each claim derives from an authorized source can significantly ease compliance burdens. For instance:
- If your financial statements summarize a quarterly PDF report, the attestation can confirm that the summary aligns with actual figures in that PDF.
- If your technical research cites specific pages from an external knowledge base, the attestation shows your references match relevant phrases in the original text.
Zero-Trust Environments
Zero-trust architecture demands that every element of your system—and the data flowing through it—be independently verifiable. Digital attestations slot neatly into this mindset. They act as a self-contained seal of authenticity, using cryptographic signatures to validate the origin and integrity of your content.
Key Features of an Effective Digital Attestation System
1. Cryptographic Signing
At the heart of any digital attestation is cryptographic signing. By using a private key (often stored securely via services like AWS Key Management Service, or KMS), each attestation is sealed so that altering the content or source reference breaks the signature. Anyone with the corresponding public key can verify that the attestation is intact.
Why it matters:
- Tamper-Evident: A changed analysis or source URL would invalidate the signature.
- Portable: The signed JSON can be stored anywhere—on GitHub, in Amazon S3, or locally—without losing its verifiability.
2. Source Verification and Scoring
A digital attestation isn’t just a statement of “we have a reference.” It’s also a proof that your content genuinely reflects the source. This proof can involve multiple checks:
- Token Overlap: Compares word usage between your analysis and source text, adjusting for stemming so that “deploy” and “deployment” are recognized as similar tokens.
- Phrase Matching: Identifies consecutive word sequences that appear in both texts, even if paraphrased.
- Domain Relevance: Looks for domain-specific terms—“cloud,” “infrastructure,” “revenue,” “compliance,” etc.—to confirm the analysis is on-topic.
- Threshold Scoring: Combines these metrics into a weighted score and flags the analysis as verified (or not) once it crosses a user-defined threshold.
Why it matters:
- Measurable Assurance: It’s more than a hyperlink. You see objective metrics indicating how closely the analysis aligns with the source.
- Fine-Tuning: Adjustable thresholds let teams balance strict or more flexible verification rules.
3. Handling PDF and Offline Documents
Not all sources are on the Internet. PDF files dominate many organizational workflows—financial reports, academic papers, compliance documents, etc. A robust attestation system includes:
- PDF Text Extraction: Automatically reads each page (using tools like PyPDF2).
- Error Handling: Gracefully manages corrupted PDFs or non-textual documents.
- Offline Support: Works with local file paths, which is crucial for sensitive or proprietary documents that aren’t accessible online.
Why it matters:
- Broad Applicability: Capture references from documents that only exist behind corporate firewalls or are not publicly available.
- Research-Grade: Perfect for labs, academic institutions, or regulated industries that rely on PDF-based publications.
4. Badge Generation for Quick Verification
Sometimes you need an at-a-glance indicator of whether an analysis is verified. That’s where simple badge-generation services—like Shields.io—come in. The system:
- Produces a URL to a colored badge (green for verified, red for unverified).
- Embeds a shortened version of the attestation ID (or hash) directly into the badge for easy cross-referencing.
- Can be inserted into README files, wikis, or dashboards so that viewers instantly know if your content checks out.
Why it matters:
- Accessible Feedback: Non-technical stakeholders see a green or red badge, giving them a confidence checkpoint without digging through logs or JSON files.
- Simplicity: It’s easy to share or publish, which encourages adoption across teams.
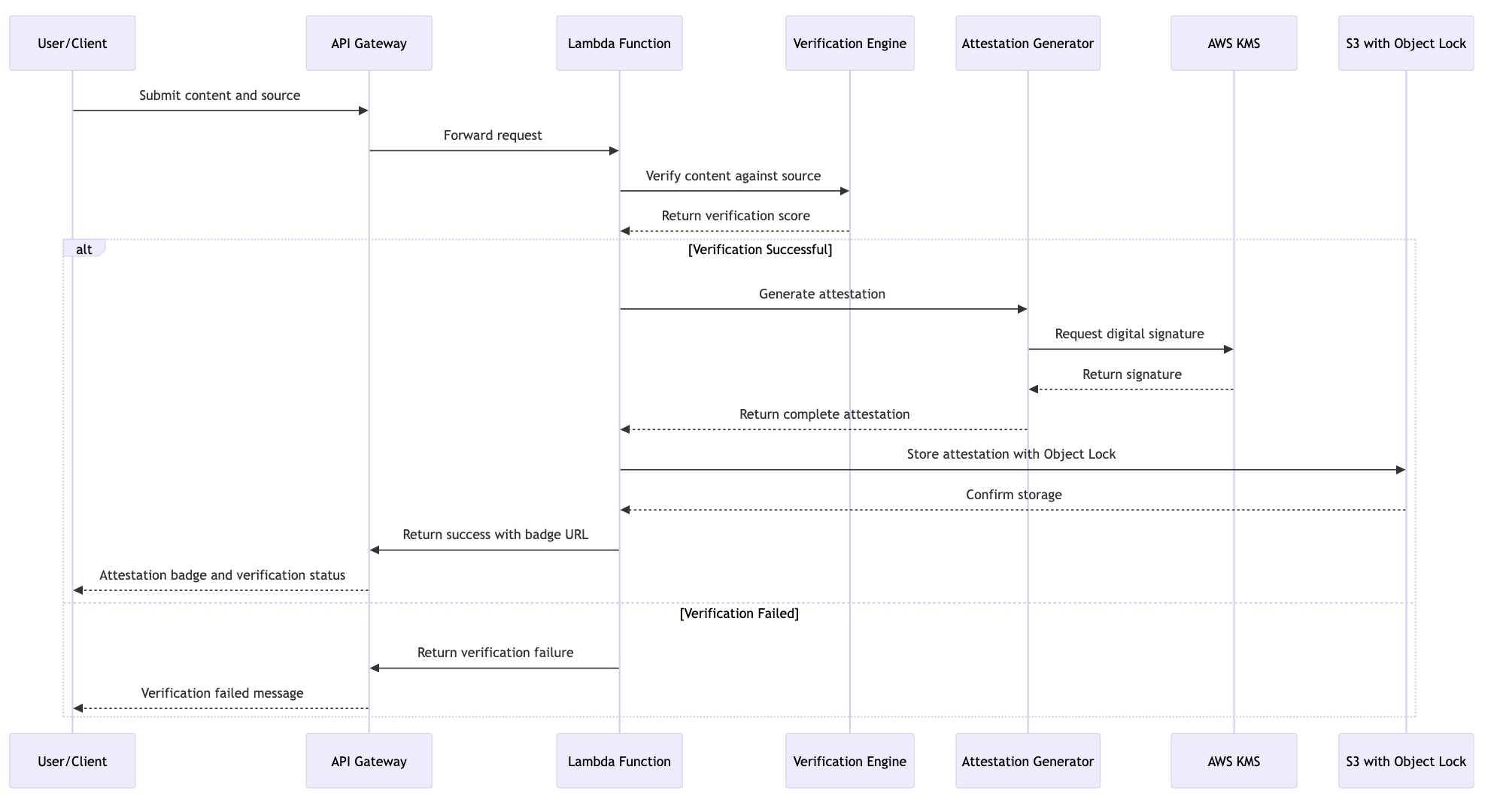
5. AWS Integration for Security and Scale
For organizations running on AWS, a natural next step is to deploy this verification system in a cloud-native way:
- AWS Lambda: A serverless function can handle requests to generate or verify attestations on-demand.
- Amazon S3 with Object Lock: Store the signed attestations in a WORM (Write Once, Read Many) mode, ensuring no one can delete or alter them for the duration you specify.
- AWS KMS for Keys: Secure key management with access controls and automatic rotation.
- AWS CloudTrail Auditing: Every signing request or verification attempt can be logged for a full audit trail.
Why it matters:
- Scalability: Whether you’re verifying a single PDF or thousands, AWS automatically handles varying loads.
- Security: Minimizes your attack surface by offloading cryptographic tasks and immutability to cloud services.
6. Future-Oriented Enhancements
Once your attestation system establishes trust in textual references, you can layer on more advanced features:
- Quote Extraction and Citation
- Extract verbatim quotes from the source.
- Auto-generate citations.
- Enforce max quote lengths for regulatory or fair-use compliance.
- Visual Source Capture
- Capture screenshots of a webpage or PDF at the moment of attestation.
- Store screenshots alongside a tamper-evident hash, proving exactly what the source looked like when you cited it.
- Hosted API with Large File Support
- Use presigned S3 URLs to handle file uploads up to several gigabytes.
- Integrate with large-scale enterprise systems, letting them programmatically verify massive documents or entire knowledge bases.
Why it matters:
- Holistic Proof: Goes beyond textual matching; you end up with a “snapshot in time,” covering both textual and visual evidence.
- Compliance Gold Standard: Perfect for regulated environments where a text-based reference isn’t enough—capturing screenshots or quotes ensures bulletproof evidence.
Example: Verifying a Financial Summary from a PDF
Imagine you’re creating a quarterly report summarizing last year’s revenues. The source is a 50-page PDF with details on each department’s performance. Here’s how the attestation process might work:
- Analysis Input: “According to the Q4 report, revenue grew by 15% year-over-year, with cloud services seeing the biggest gain at 20%.”
- Extraction & Verification:
- The attestation tool scans the local PDF, extracting text from each page.
- It calculates token overlap for phrases like “revenue grew by 15%” and “cloud services” across the PDF’s text.
- Scoring & Signing:
- If the score is above your threshold (say, 0.3), the system marks it as verified.
- It generates a JSON payload with a unique attestation ID, timestamp, source reference (./financial_report.pdf), and your analysis text.
- This payload is then cryptographically signed, so any change (e.g., changing “15%” to “25%”) invalidates the signature.
- Badge Output:
- The system creates a green badge showing the short attestation ID.
- In your final PDF or README, you embed the badge so readers can confirm that your summary truly matches the original document.
You can see an illustration of this process in a sequence diagram below.
Revisiting the Opening Quote
In my introduction, I demonstrated how the digital attestation engine can conclusively prove that an analysis is derived from a specified source link. For context, Amazon’s Leadership Principles articulate that “Leaders are right a lot. They have strong judgment and good instincts. They seek diverse perspectives and work to disconfirm their beliefs.” My interpretation of this principle was: “Leaders blend strong judgment and instincts with active self-scrutiny—seeking diverse perspectives and challenging their assumptions—to stay both accurate and adaptable.”
To verify that this interpretation was indeed rooted in the original source, I ran it through our digital attestation engine using the command shown below.
./run.sh verify https://www.amazon.jobs/content/en/our-workplace/leadership-principles 'Leaders blend strong judgment and instincts with active self-scrutiny—seeking diverse perspectives and challenging their assumptions—to stay both accurate and adaptable.'As illustrated in the figure below, the engine confirmed that the analysis was based on the source, generating a tamper-proof dataset complete with a digital signature and public key. Digital signatures in the attestation system use a secure private key to mathematically bind the payload (content, source URL, timestamp). The accompanying public key verifies the signature’s authenticity and integrity.
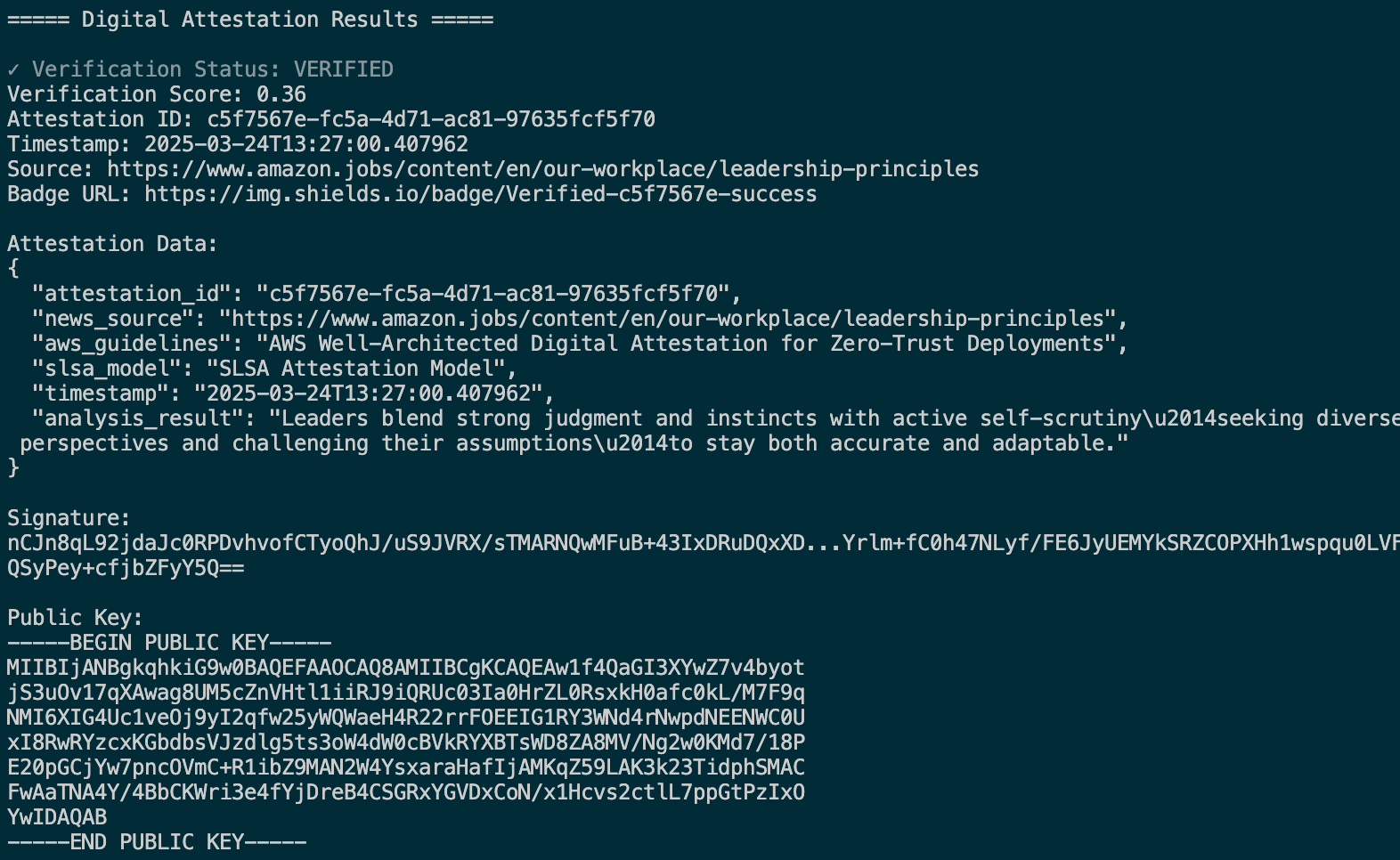
The engine also produces a visual digital badge—displaying the initial portion of the digital signature—that points to a secured data repository leveraging Amazon S3 Object Lock, creating an immutable audit trail.

Next, I repeated this process for an “analysis” that was intentionally not derived from the source, using the command below.
./run.sh verify https://www.amazon.jobs/content/en/our-workplace/leadership-principles 'Sharing is Caring and is about judgement and being right'As shown in the resulting figure, the engine was unable to verify its authenticity. While it still created a unique digital signature and public key, it clearly indicated that this interpretation was unverified.
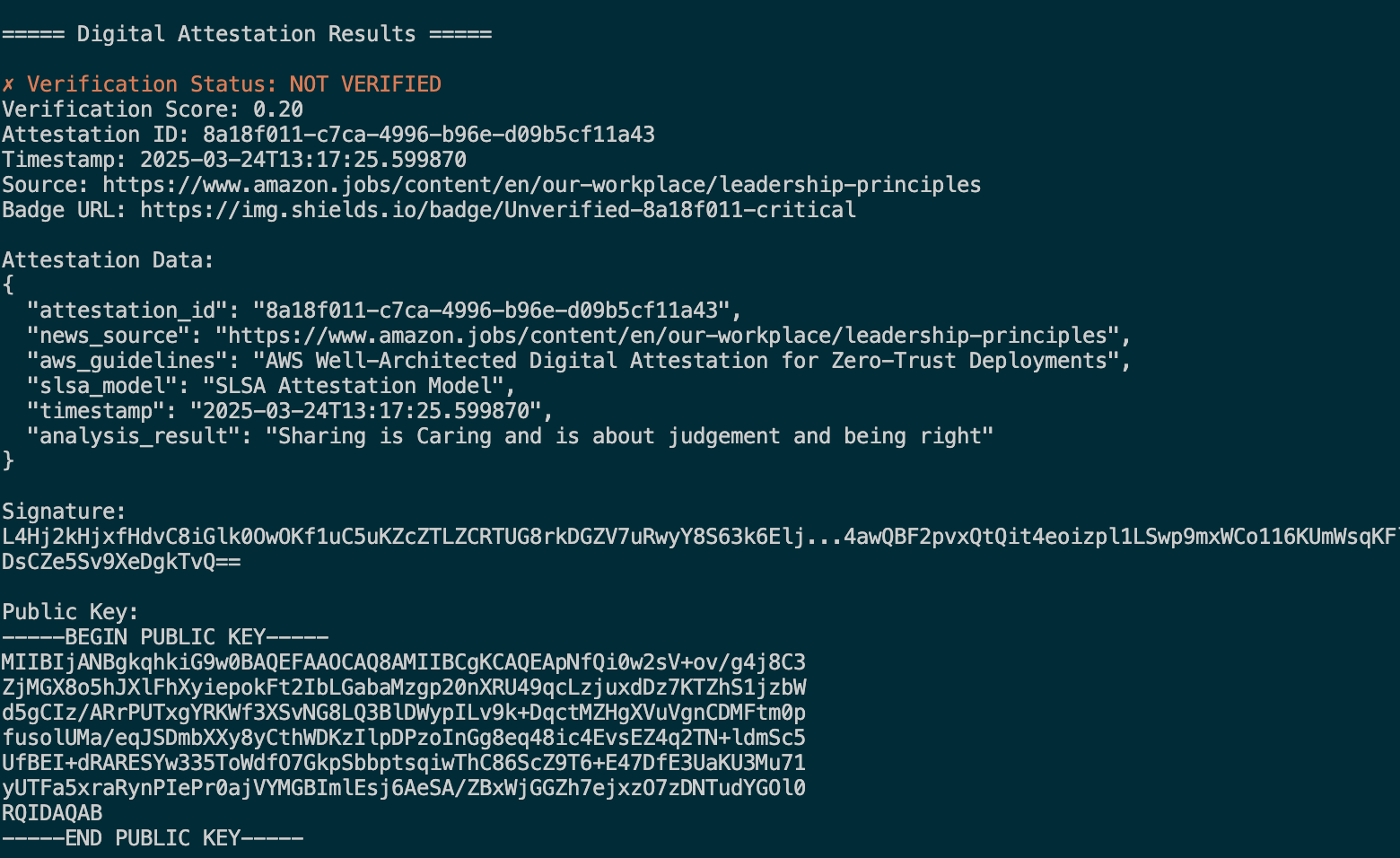
The digital badge, once again linking to a locked S3 object, corroborated the lack of legitimate provenance by displaying the incomplete—and therefore unconfirmed—signature data.

Here's a code snippet showing how it's verifying the text based on the source.
def verify_text_based_on_source(source: str, analysis_text: str, threshold: float = 0.3) -> (bool, float):
"""
...
"""
from urllib.parse import urlparse
is_url = bool(urlparse(source).scheme)
if is_url:
source_content = _fetch_url_content(source)
else:
if source.lower().endswith('.pdf'):
source_content = extract_text_from_pdf(source)
else:
with open(source, 'r', encoding='utf-8') as file:
source_content = file.read()
if not source_content:
return False, 0.0
token_overlap_score = _calculate_token_overlap(source_content, analysis_text)
phrase_match_score = _calculate_phrase_match(source_content, analysis_text)
concept_match_score = _calculate_concept_match(source_content, analysis_text)
combined_score = (
0.4 * token_overlap_score +
0.4 * phrase_match_score +
0.2 * concept_match_score
)
return (combined_score >= threshold), combined_scoreVerify the Analysis Text is Based on the Source
Here's a snippet on creating an attestation and digital signature.
def create_and_sign_attestation(news_source: str, analysis: str) -> dict:
# 1. Generate RSA keys (for demonstration only)
private_key, public_key = generate_keys()
# 2. Create the attestation payload
attestation_payload = create_attestation(news_source, analysis)
# 3. Sign the payload with the RSA private key
signature = sign_payload(attestation_payload, private_key)
# 4. Add the signature and public key (PEM format) to the attestation
attestation_payload["signature"] = signature
attestation_payload["public_key"] = public_key.public_bytes(
encoding=serialization.Encoding.PEM,
format=serialization.PublicFormat.SubjectPublicKeyInfo
).decode('utf-8')
# 5. Return the complete attestation (payload + signature + key)
return attestation_payloadCreate an Attestation and Digital Signature
Through these examples, it’s evident that the digital attestation engine provides a transparent chain of trust for any textual analysis. By embracing mechanisms like this—and by actively seeking diverse perspectives and challenging our own views in line with Amazon’s Leadership Principles—we can operate with greater confidence in the integrity of our data, maintaining rigorous standards for accuracy and reliability.
Trust as a Competitive Advantage
In a world moving ever faster, trust is a differentiator. When you integrate digital attestations into your CI/CD pipelines, documentation, or internal processes, you instantly convey credibility. Teams no longer ask, “Is this data correct?” or “Did we misquote the source?” because verification is automatic and auditable.
- Cross-Team Confidence: Developers, analysts, and compliance officers share a consistent source of truth, accelerating decision-making.
- Seamless Audits: Regulatory bodies or external reviewers can re-check the attestation themselves. The cryptographic signature is proof that no one has tampered with references or statements.
- Simple, Automatable Workflows: A single command-line interface or hosted API can handle both generation and verification—making it straightforward to fit into existing deployment or research pipelines.
Putting It All Together
By focusing on cryptographic signing, source verification, PDF handling, badge generation, and scalable cloud deployment, you achieve a complete solution for bridging the gap between “citing a source” and “proving the authenticity of a source.” Whether you’re a researcher citing a new academic paper, a software engineer referencing AWS docs, or a financial analyst summarizing quarterly reports, a robust digital attestation system offers:
- Proof at a Glance: A user-friendly badge or quick verification score.
- Data Integrity: Blockchain-level trust without necessarily depending on a blockchain.
- Regulatory Alignment: An immutable, tamper-evident record that stands up to compliance checks and audits.
As the industry evolves toward more transparent, secure, and regulated content workflows, digital attestations serve as an accessible, future-proof way to demonstrate that your text stands on the firm ground of an authentic source. Whether you keep it simple with textual verification or go deeper by capturing screenshots for maximum fidelity, digital attestations raise the bar for how we reference other materials—and why our audiences should believe us.
By embedding cryptographic verification at the heart of every reference, you build trust in every paragraph, chart, or conclusion you publish.
Further Reading
- AWS Well-Architected Digital Attestation for Zero-Trust Deployments
- SLSA (Supply chain Levels for Software Artifacts)
- Shields.io for generating verification badges
